Your New Gear Is Broken

Some folks relish the unboxing of a new phone, computer, or smart device. For me, it causes a little bit of anxiety. While it usually means a clean slate, free of cluttered file systems, long ignored caches, and memory-hungry applications, it also means there’s work to do. Often, new devices are configured for ease of use which generally means convenience trumps security. Unwanted software, unnecessary administrative privileges, application permissions, and chatty services are the norm for an improved User Experience. I am not a fan.
Here, we’ll discuss a few pointers to help improve your device’s security by reducing the attack surface, also known as device hardening.
Trim The Fat
Get rid of the bloat! Many new Personal Electronic Devices (PED), but especially PCs and Android phones, are chock full of software that you will probably never use. These unwanted applications are called “Bloatware” and while they may not take up much space or memory:
1) You probably don’t need three text-messaging options or four trial subscriptions to music streaming services.
2) You can spend the extra two minutes to locate and download Candy Crush if you want it.
3) Left alone, those bloatware applications could become devastating attack vectors.
When developers update software, they often include security patches to address previously discovered vulnerabilities, and if these apps simply live on your machine and are never updated, you risk having well-known vulnerabilities that can be easily exploited. Save your space, recover your memory, and protect yourself by purging unnecessary and unwanted applications.
Tips To Harden Your Devices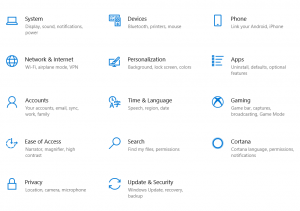
Create and use non-admin accounts – By default the first user account on most computers is also a local administrator, which is basically “God mode” or “Super user” and that can affect the entire system. This account can install software, create new accounts, manage permissions globally, and configure, enable, or disable privileged applications and services. If your machine is compromised while using this account, you’re giving all the keys to the castle to the attacker. Instead, create a local user as your primary account and escalate your privileges when prompted by the system. That way, you can reduce the impact of a successful hostile takeover. While you’re at it, you should delete or disable unused or guest accounts to help minimize that attack surface.
Review sharing – Just take a minute and review the settings for file, printer, and network sharing. These are usually locked down by default, but certain bloatware linked to other software could borrow permissions and affect sharing rules.
Add another password – When powering on, your machine uses a bootstrap process controlled by either a legacy BIOS or the more modern UEFI. Within the BIOS/UEFI there are several menus and options that can impact several critical system settings like system time, Secureboot, mounted partitions, and boot order. This can be catastrophic if compromised. For example, if your boot order is changed, an attacker can circumvent your Operating System and gain access to your unencrypted filesystem with only a USB or DVD. You can prevent or at least deter tampering with these settings by creating a BIOS/UEFI password.
**Note** You can find the easiest method to access your device’s BIOS/UEFI by searching online. It may be something like pressing the F2 or F11 key during the boot process, or holding down a button while restarting the machine, or on some smartphones powering up while pressing the volume down and power buttons simultaneously.
Security Best Practices
On top of these hardening tips, you’ll want to follow-up with standard security practices, like:
- Use complex passwords or biometrics for account access.
- Enable screen lock after a short period of inactivity.
- Review your OS settings, like disabling geolocation services, application permissions, and the device assistant (Siri, Okay Google, Cortana, etc.) to suit your security needs.
- If available, enable Full Disk Encryption (e.g. Bitlocker, FileVault). If unavailable, you can still create an encrypted vault, volume, or partition with open source tools like Veracrypt.
- Enable automatic updates for software and the Operating System.
- Install and configure a secure browser.
- Enable or install Anti-Virus Software.
- Invest in a trustworthy VPN.