This week’s blog will provide a few quick and incredibly easy tips to support the National Cybersecurity Awareness Month’s weekly topic “If it’s connected, protect it”. Taking just two minutes to manage your updates, enable MFA, and switch on a VPN client could pay dividends in boosting your cyber security posture.
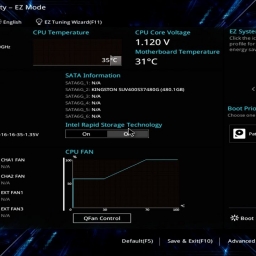
Updates

We talk about this tip often, especially in our Hardening Endpoint Devices blog, but one of the easiest steps to improve the protection of your Internet-connected devices is to simply enable automatic software updates. These updates are not just meant to improve device performance or add new features, but to address and install important security patches. These patches often fix any recent bugs, issues, or vulnerabilities that have been discovered since the latest update, so skipping them possibly leaves your devices open to well-known attacks. Do not forget the less obvious connected devices, like Smart TVs and streaming boxes, gaming systems, IOT hubs, routers, and wearables. As long as they’re on your network, you’ll want to ensure they are using the most up-to-date software or firmware available.
Complex Passwords and MFA

Passwords are often the weakest link in any secured system. They’re vulnerable to compromise through social engineering, shoulder surfing, cracking attacks, and a number of other techniques popular with hackers and criminals. Using long and complex passwords can shore up your defensive posture, and this is easily achieved using password managers like Lastpass or 1Password which can create, store, recall, and audit your various accounts’ passwords. But the surest way to increase your security is to enable Multi-factor authentication (MFA) or 2-factor authentication when it’s available. This way you are protected in the event of a data breach because attackers will need both your password and that SMS- or email- code, physical token, or whatever MFA solution or service you are using.
VPN

We go into lots of detail to secure your Wi-Fi router here, but an absolute must-have for travelers, road-warriors, and users who must rely on public Wi-Fi, is a Virtual Private Network (VPN). A VPN establishes an encrypted tunnel from your device to your VPN server, providing an additional layer of protection for your Internet traffic against Wi-Fi sniffing or other eavesdropping attacks. But VPNs are not just for the road. You can also defend against your Internet Service Provider (ISP) monitoring, logging, and potentially selling your personal browsing history. To boot, VPNs help obfuscate your location to websites by masking your personal details (i.e. your Public IP address), and some users find them useful to circumvent administrative or censorship blocks (. e.g. the great firewall).
Phishing
If there is any doubt about the authenticity of an email’s sender, any hesitation at all, do not open that email! Almost a third of confirmed data breaches include some sort of fake emailing campaign to trick or elicit information from an unsuspecting victim. Modern email providers offer some protection against these phishing attacks, but you are the last line of defense against these popular victim-triggered attacks.
Looking for more? Below are additional posts where we go a little more in depth with extra steps you can take to help lock down your personal and business devices.
https://ops-tech-alliance.com/how-to-protect-your-stored-data/
https://ops-tech-alliance.com/passwords-and-alternate-authentication-methods/
https://ops-tech-alliance.com/virtual-private-networks-and-privacy/