What is Ransomware
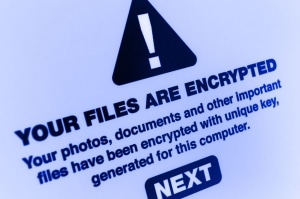
To most people, being held at ransom sounds like something that could only happen in a Hollywood movie. We’ve all seen the stories where a person gets kidnapped and held hostage, while the villain demands money in exchange for the hostage’s freedom. The good news is this scenario will probably never happen to you. The bad news is you are increasingly likely to be the victim of a different kind of hostage situation. In today’s cyber world, your computer and its data could be held hostage due to a ransomware attack.
Ransomware is a type of malware that prevents or blocks you from accessing your computer data or system, usually through encryption or a lock screen. Like with many other malware and scam attacks, malicious emails are the most common vehicle used to deliver ransomware. The hackers demand money from their victims in exchange for the decryption key that will grant access to the computer data. The ransomware will often threaten to either delete or release the data publicly if the ransom is not paid within a specific time frame. Of course, criminals cannot be trusted so there is no guarantee that you will regain access to your computer data after paying the ransom.
Recent Attacks in the News

Hackers also have their sights set on much larger targets than the average home user. Businesses and governments are increasingly being attacked with ransomware. New ransomware attacks are being reported on an almost daily basis. Last month, a major U.S. fuel pipeline was forcibly shut down by a ransomware attack for 11 days. The attack and the ensuing panic led to gas shortages across the east coast. A ransom of over 4 million dollars’ worth of bitcoin was paid to the hacker group known as Darkside to finally end the shutdown. This attack is the largest and most successful attack on the U.S oil infrastructure.
It was reported this month that a key tech vendor for Congress has become the victim of a ransomware attack. The software company known as iConstituent provides services for Congress that allows users to “easily connect with constituents, collaborate on casework, and manage internal and external communications”. The services have been unavailable to nearly 60 House offices in Congress for several weeks with no end to the situation in sight. Clearly, the reach of ransomware attacks should not be underestimated by anyone. Unless cyber security is taken more seriously by everyone, these attacks will continue to escalate.
Tips for Preventing Ransomware Attacks
As I mentioned earlier, malicious emails are the most common vehicle to deliver ransomware. This could be in the form of an email attachment or a malicious URL. In our blogs, we have stressed the importance of good cyber hygiene and I will leave you with a few tips to avoid falling victim to ransomware attacks.
- Do not open emails from suspicious sources or click suspicious links. Examine the emails carefully for any sign of fraudulence. Always verify the sender’s email address.
- Always keep a backup of your data. (I have backups of backups of my kids’ baby pictures. Storage media and cloud storage services are cheap, these memories are irreplaceable)
- Do not connect unknown media to your devices. Finding that flash drive on the ground may not have been good luck.
- Keep your operating system, anti-virus software, and other applications updated. Many malware attacks are caused by known vulnerabilities left unpatched.
- Only use trusted download sources. Never download anything from an unknown source.