Microsoft vs TrickBot

There has been a lot of news recently about the TrickBot bot network, one of the largest botnets in use today with over a million infected machines. A botnet is a distributed network of devices that have been infected by malware and are under centralized control–someone else has the keys to your device, and they’re driving. This army of machines can then be used or even rented by criminals to conduct illegal activities like harvest data, attack websites and online infrastructure, and further propagate malware to build the botnet even larger. The recent TrickBot news was that Microsoft and several other vendors won a court decision to try and legally take down the network. Researchers investigated TrickBot incidents, analyzed some of its malware code, enumerated the network’s Command and Control (C2) nodes, and had those servers taken offline to effectively cut the head off of the snake. Unfortunately, the takedown of TrickBot didn’t quite stick, as the network proved to be quite resilient, so Microsoft and team started planning their next move.
How Could This Happen To Me?

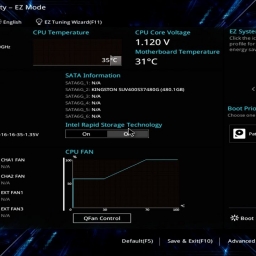
My first exposure to a botnet was maybe a decade ago, when I was able to attend a pretty unique offensive cyber operations course, led by instructors with decades of experience in both private and public cyber security. During the first week of class, the lead instructor was complaining about spotty performance and sluggishness of his home network but because class was underway he didn’t have much time to troubleshoot until the weekend. He returned on Monday, rightfully exasperated, and explained that he had discovered that his teenage son’s laptop had been compromised and turned into a bot supporting an illegal botnet. This was back in the era of Limewire and other peer to peer sharing, and his son had evidently picked up some malware while pirating video games. Once infected, his gaming laptop called back to the C2 node which hijacked a small partition of that computer’s disk drive, and ran additional background services to unwittingly deliver massive amounts of spam email to strangers, bogging down his network. The instructor was flummoxed. “How could this happen to me and my house?”, you could see it on his face.
The issue with modern botnets like TrickBot is that they aren’t necessarily victim-initiated. That is, they don’t require a deliberate download or install to infect your device. Many of these attacks are automated by crawlers and spiders that systematically “poke” every device they find. If your device is “poked” and determined to fit a particular profile, and you’ve skipped over some basic cyber security practices, your device could become infected while you’re asleep in the next room.
Don’t Become A Zombie
Well, Cyber Dad™ laid down a few new ground rules for his kids and their online activities, which are just good ideas for everyone to defend against becoming another zombie in a botnet:
- Don’t pirate
- Only download software, files, etc. from trusted sources
- Enable or install antivirus software and keep it up to date
- Ensure that auto-update is on for all software, drivers, and the Operating System
- If you’re experiencing something unusual, tell someone. That is, Cyber Dad™ can’t fix what he doesn’t know about.
For dad’s part, he stepped up his game by installing a Network Security and Intrusion Detection System like Bro/Zeek https://zeek.org/ to monitor netflow and unusual behavior, and then he made some new firewall rules to prevent unwanted inbound AND outbound traffic.